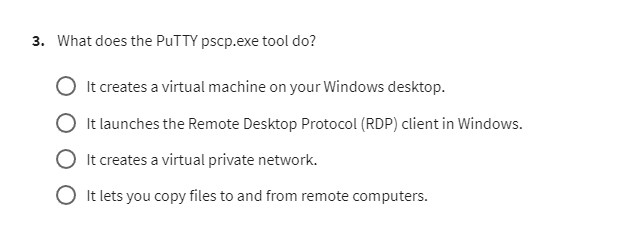
The PuTTY secure copy client, often known as pscp.exe, is a command-line tool that lets users securely copy files between a local computer and a remote computer. It uses the Secure Shell (SSH) protocol to ensure that all file transfer via SSH is encrypted and safe from spying eyes.
Image Source: media.cheggcdn.com
Deciphering the pscp Command Line Tool
The pscp.exe program is part of the larger PuTTY suite. While many users know PuTTY for its graphical terminal interface, pscp is its counterpart designed specifically for automated or command-line based file movement. Think of it as a secure version of the standard copy or move commands, but for network connections. It is a vital tool for system administrators and developers who frequently manage files on remote servers.
Core Function: Secure File Transfer via SSH
The primary job of the pscp command line tool is to move files across networks securely. It works by establishing an SSH connection to the remote host. Once the secure channel is open, it transfers the files. This is much safer than older protocols like FTP, which send data in plain text.
The security aspect is key. Because it relies on SSH, pscp handles authentication using passwords or key files, just like the main PuTTY application. This means your login details and the file contents are protected during transit.
Why Use pscp Instead of Other Tools?
Many operating systems, like Linux and macOS, have a built-in scp command. However, for users primarily on Windows, pscp.exe fills that gap perfectly. It acts as a native Windows SCP client.
Here is a quick look at why people choose pscp:
- Security: Uses strong SSH encryption.
- Simplicity: The command structure is straightforward once you learn the syntax.
- Integration: Works seamlessly with other PuTTY tools (like
plinkor the main PuTTY GUI). - Automation: Because it is a command-line tool, it can be easily put into batch scripts (
.batfiles) for scheduled or repetitive tasks.
Key Use Cases for the pscp Executable Function
The pscp executable function centers entirely around moving data. However, this simple action has many important applications in daily computing and system maintenance.
Transferring Files to a Remote Server (Uploading)
The most common use is uploading files from your local machine to a remote server. Imagine you have finished updating a website file locally and need to put it onto your web host.
The basic syntax for uploading is:
pscp [options] local_file user@remote_host:remote_path
Example Scenario:
You have a file named report.pdf on your desktop (C:\Users\You\Desktop) and need to upload it to the /home/john/documents folder on a server named myserver.com.
pscp “C:\Users\You\Desktop\report.pdf” john@myserver.com:/home/john/documents/
This command asks for John’s password for myserver.com and then securely copies the file across.
Downloading Files from a Remote Server (Downloading)
Conversely, you might need to pull configuration files or log data from a remote machine back to your local drive.
The syntax for downloading is slightly different; you put the remote location first:
pscp [options] user@remote_host:remote_file local_path
Example Scenario:
You need to get the error log (server.log) from the /var/log directory on myserver.com and save it to your local Downloads folder.
pscp john@myserver.com:/var/log/server.log “C:\Users\You\Downloads\”
Copying Files Between Two Remote Hosts
One powerful, often overlooked feature of the PuTTY secure copy client is the ability to copy a file directly from one remote server to another, without the file ever passing through your local machine. This is efficient for server maintenance.
The syntax requires you to specify both remote hosts:
pscp [options] user1@host1:remote_file user2@host2:remote_path
This operation still requires your local machine to handle the initial authentication handshake for both servers.
Exploring PuTTY Secure Copy Usage: Options and Parameters
To use pscp effectively, you must know its common switches or options. These options modify how the file transfer behaves, affecting security, transfer mode, and error handling.
Essential Command Line Switches
Here is a table summarizing some of the most frequently used flags when using pscp for SFTP or standard SCP transfers:
| Switch | Description | Purpose |
|---|---|---|
-P port |
Specifies the port number. | Use if the remote SSH server is not running on the default port 22. |
-l username |
Specifies the login name. | Useful if you do not want to type the username every time. |
-pw password |
Provides the password on the command line. | Caution: Generally avoided as it leaves the password in plain text history. |
-i identity_file |
Specifies the private key file. | Essential for key-based authentication. Must be a PuTTY private key (.ppk file). |
-r |
Recursive copy. | Used to copy entire directories and their contents. |
-q |
Quiet mode. | Suppresses the progress meter and non-error messages. |
-v |
Verbose mode. | Shows detailed output about the connection and transfer process, useful for troubleshooting. |
Handling Directories with -r
When you need to move an entire folder structure, the -r (recursive) switch is mandatory. Without it, pscp will fail if you point it at a directory name.
Uploading a directory:
pscp -r C:\MyProjectFiles john@webserver:/var/www/html/
This copies MyProjectFiles and everything inside it to the /var/www/html/ directory on the remote server.
Using Private Keys for Authentication
For security and automation, relying on passwords is poor practice. Instead, system administrators use SSH key pairs. If you have generated a private key using PuTTYgen and saved it as mykey.ppk, you use the -i switch.
pscp -i C:\Keys\mykey.ppk local_data.zip john@dbserver:/backup/
This command attempts to connect to dbserver using the credentials stored in mykey.ppk. This allows scripts to run without requiring manual password input.
Grasping the Role of Secure File Transfer Protocol (SFTP)
While pscp is primarily a Secure Copy Protocol (SCP) client, its functionality overlaps significantly with SFTP (Secure File Transfer Protocol). Both operate over SSH, ensuring security.
SCP vs. SFTP: A Key Distinction
Historically, SCP was simpler and sometimes faster for raw file copying. SFTP, however, is more feature-rich. It allows for directory listings, renaming, and deleting files remotely, functionalities that standard SCP traditionally did not support directly within the transfer command itself.
When you use the pscp command line tool, you are explicitly invoking the SCP protocol. PuTTY also offers an SFTP client, which is a separate executable called psftp.exe.
If your goal is only to push or pull a file quickly and securely, pscp is ideal. If you need interactive management of files on the remote side (like checking if a file exists before overwriting it), the separate psftp client might be more appropriate. However, pscp is designed to be a quick, non-interactive remote file transfer utility.
Why is it called the PuTTY secure copy client?
It’s named this way because it adheres to the SCP standard, which runs over the SSH transport layer provided by the PuTTY framework. This heritage links it directly to the core security and connection methods established by the main PuTTY application.
Advanced Topics in pscp Usage
Moving beyond basic uploads and downloads requires utilizing more nuanced features of the tool.
Handling File Names with Spaces or Special Characters
If your local or remote file path contains spaces, you must enclose the entire path in double quotes ("). This is standard practice for most command-line tools. Failure to quote paths correctly is a common reason for pscp errors.
Checking Connection and Authentication Errors
When a transfer fails, the output from pscp is crucial. Using the verbose mode (-v) provides extensive information about the connection handshake.
Common errors you might see include:
- “Server refused our key”: Your private key file (
.ppk) is not accepted by the server. Check the file permissions or ensure the public key is correctly installed on the server’sauthorized_keysfile. - “Access denied”: This usually means the username or password provided was incorrect, or the remote user does not have permission to write to the specified remote directory.
- “Connection timed out”: A firewall is likely blocking the SSH port (usually 22), or the remote server is offline.
Integrating pscp into Windows Batch Scripts
The true power of this command line SCP client on Windows emerges when it is scripted. System administrators use batch files to automate backups or deployment processes.
A simple backup script using pscp might look like this:
@echo off SET LOCAL_PATH=C:\DailyBackups SET REMOTE_HOST=backup.mycompany.com SET REMOTE_USER=admin SET REMOTE_DIR=/srv/data/ SET KEY_FILE=C:\Keys\backup_key.ppk ECHO Starting secure backup copy… pscp -q -i %KEY_FILE% %LOCAL_PATH%\important_data.zip %REMOTE_USER%@%REMOTE_HOST%:%REMOTE_DIR% IF %ERRORLEVEL% EQU 0 ( ECHO Backup successful at %DATE% %TIME% ) ELSE ( ECHO Backup failed! Check the error output above. )
This script automates the process, ensuring files are moved securely without manual intervention, showcasing the utility of the pscp executable function in automation workflows.
Security Considerations When Using pscp
Although pscp provides security through SSH encryption, how you use the tool introduces potential vulnerabilities. Secure deployment requires awareness of these risks.
Protecting Private Keys
If your private key file (.ppk) is compromised, an attacker can impersonate you to any server where that key is authorized.
Best Practices:
- Password Protect Keys: Always use a strong passphrase when generating keys in PuTTYgen. This passphrase is required every time the key is used, even in automated scripts (though this complicates scripting).
- Limit Key Permissions: On the local machine, ensure the directory containing the key file is only accessible by necessary users.
- Server-Side Restrictions: On the remote server, restrict what the key can do. For instance, you can configure the
authorized_keysfile to only allow that specific key to run certain commands or transfer files to a specific directory.
Avoiding Command Line Passwords
As noted earlier, never embed passwords directly in command-line arguments using the -pw switch, especially in scripts stored on shared systems. This exposes the password in the system process list and shell history files. Key-based authentication (-i) is the preferred, secure alternative for non-interactive use.
Understanding File Permissions During Transfer
When using pscp to upload a file, it generally tries to preserve the file’s original permissions from the local system. However, the final permissions on the remote server are also dictated by the remote user’s umask setting and directory permissions. If you need very specific permissions set upon arrival, you may need to follow up the transfer with an SSH command (using plink or the main PuTTY GUI) to run the chmod command on the remote file.
Comparing pscp to Alternative Windows SCP Clients
While pscp is robust, Windows users have other options for remote file transfer utility needs. Comparing it helps illustrate where pscp fits best.
Graphical Clients (e.g., WinSCP)
Graphical clients are excellent for beginners or for exploratory file management. They offer drag-and-drop interfaces and built-in SFTP/SCP support, often combining viewing and transferring in one window.
- Advantage: Easy to use, visual representation of both local and remote file systems.
- Disadvantage: Poor for scripting and automation.
PowerShell Built-in cmdlets
Modern versions of Windows now include native PowerShell commands for interacting with SSH, such as Copy-Item with SSH transport capabilities.
- Advantage: Native to the modern Windows environment, requiring no third-party installs.
- Disadvantage: May lack some highly specific features found in the long-established PuTTY suite, and compatibility might vary across older Windows versions where PuTTY remains reliable.
Why Stick with pscp?
The PuTTY secure copy client remains popular because it is lightweight, extremely reliable across decades of use, and perfectly suited for shell scripting environments common in system administration tasks where a GUI is impractical or impossible. Its simple interface perfectly supports the core requirement: secure, one-off file transfers initiated from the command line.
Frequently Asked Questions (FAQ)
Q: Can I use pscp to transfer files over a non-standard SSH port?
A: Yes, absolutely. You use the -P switch followed by the port number. For example, to connect to port 2222: pscp -P 2222 localfile user@host:/remote/path.
Q: Does pscp support SFTP directly, or only SCP?
A: The pscp command line tool strictly uses the SCP protocol over SSH. If you need SFTP features (like directory browsing or file deletion commands), you should use PuTTY’s companion tool, psftp.exe.
Q: What do I do if my private key file is in PuTTY’s .ppk format?
A: This is the expected format. You use the -i switch to point directly to the .ppk file. pscp is designed specifically to read these files for key-based authentication when operating as a Windows SCP client.
Q: Is it safe to use pscp from a scheduled task in Windows?
A: Yes, it is safe and highly recommended, provided you use key-based authentication (-i) instead of embedding passwords. Scheduled tasks are a prime use case for the pscp executable function in automated maintenance routines.
Q: How do I see the progress of a large file transfer with pscp?
A: By default, pscp shows a progress meter. If you do not see one, ensure you are not using the quiet mode switch (-q). Using the verbose mode (-v) will show detailed connection information alongside the transfer status.