The purpose of the emergency access tool is to provide authorized personnel with a method to quickly gain entry or control over a system, door, or device when normal access methods fail due to power loss, malfunction, or other critical situations.
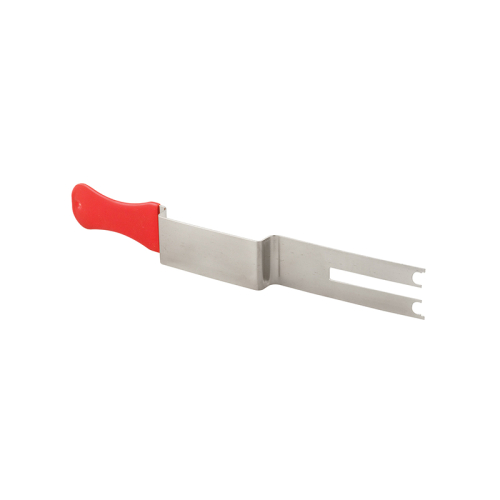
Image Source: fhc-usa.com
The Core Function: Ensuring Business Continuity
Every organization relies on systems to operate. When these systems fail, even for a short time, big problems can happen. The emergency access tool exists to stop these small problems from becoming huge, system-stopping disasters. Its main goal is keeping things running, no matter what happens. Think of it as a backup plan for getting in when the main door lock breaks.
We need reliable ways to get where we need to go or fix what is broken right away. This tool lets key people bypass normal checks quickly. This speed is vital in real emergencies.
Emergency Access Tool Functionality Explained
The emergency access tool functionality describes exactly how these tools work. They are designed for rapid deployment and immediate effect. They are not meant for daily use. They are a last resort.
Types of Emergency Access Tools
Emergency access tools come in many forms, depending on what they are meant to open or control.
| Tool Type | Primary Use Case | Typical Mechanism |
|---|---|---|
| Mechanical Keys | Physical doors, server racks | Standard key cutting, specialized profiles |
| Electronic Overrides | Security gates, electronic locks | Magnetic cards, special access codes, physical dongles |
| Software Backdoors | Network systems, critical applications | Pre-set administrative passwords, encrypted recovery keys |
In electronic systems, this often involves specialized hardware or software protocols. For physical security, it usually means a physical key. This key has special cuts or codes that standard keys do not possess. This ensures only a few people can use it.
How It Works in Practice
When a normal lock fails, a trained person uses the emergency tool.
- Identification: The person must prove they are the right person. This often involves showing ID or knowing a secret code.
- Application: The tool is used. For a door, this is inserting the key. For a system, it might be entering a special command.
- Bypass: The tool temporarily ignores the standard security checks. It grants immediate entry or control.
- Logging: Crucially, this action must be recorded. Every use must be tracked for later review.
The Purpose of Emergency Override Key in Physical Security
The purpose of emergency override key is very specific. It deals with physical access points. These points protect sensitive areas like data centers, medical storage, or main power rooms.
Imagine a fire alarm goes off. The automatic door locks engage for safety. But the fire crew needs to get inside immediately to check equipment. The standard electronic card reader might be dead due to power failure during the emergency. This is when the override key saves the day.
The override key allows trained personnel—like facilities managers or specific security guards—to open the door manually. This bypasses the electronic system completely. This speed is life-saving in true emergencies like medical crises or active security threats.
Balancing Access with Security
A major part of designing these systems involves balancing quick access with security. We need fast entry when disaster strikes. But we must also stop theft or misuse. This balancing act defines good security policy.
Tools to Prevent Unauthorized Access
Systems often include unauthorized access prevention tools built around the emergency access function itself. These are not the emergency tool, but the protections around it.
- Limited Distribution: Only a few people get the emergency key or code.
- Secure Storage: The keys or codes are kept in locked safes, often requiring dual control (two people needed to open the safe).
- One-Time Use Codes: Some electronic overrides issue temporary codes that expire after one use or a set time.
If the emergency tool is too easy to use, it becomes a huge security hole. Therefore, tight controls are put in place to manage these powerful tools responsibly.
Emergency System Bypass Mechanisms in IT
In the digital world, emergency access means bypassing software locks. These emergency system bypass mechanisms are crucial for IT systems. If a central server locks up completely, technicians must gain access to reboot it or diagnose the failure.
In IT, this bypass might involve:
- Hard Reset Procedures: Physical buttons on servers that force a restart outside of the normal operating system.
- Recovery Partitions: Hidden parts of the hard drive used to boot the system into a safe, diagnostic mode.
- Secret Administrative Accounts: Accounts with supreme privileges that are disabled during normal operation but can be activated in an emergency.
If these mechanisms are not available, a simple software crash could shut down a hospital’s record system or a stock exchange platform for hours while waiting for a complex reset.
Security Implications of Emergency Access
Because these tools offer supreme power, the security implications of emergency access are high. Misuse of an emergency key or code can lead to serious breaches, theft, or physical damage.
If an employee with emergency access decides to misuse that power, standard audit trails might not immediately flag the action if the tool is designed to work outside those trails initially. This makes accountability critical.
We must always assess the risk: How severe would the system downtime be without this access? Is that risk higher than the risk of the tool being misused? Most organizations decide that downtime risk outweighs the misuse risk, provided controls are tight.
Managing Emergency System Credentials Securely
Managing emergency system credentials is a specialized, high-priority task. These credentials—keys, codes, passwords—are far more sensitive than regular access details.
Credential Lifecycle Management
Effective management follows a strict lifecycle:
- Issuance: Only issued after strict approval, background checks, and training.
- Storage: Stored in highly secure, monitored environments (e.g., biometric vaults, encrypted key escrow systems).
- Verification: Regular checks to ensure the person still holds the authority to possess the credential.
- Revocation: Immediate removal and replacement of the credential the moment the person leaves the role or the credential is lost.
Losing control of a master emergency key is like giving someone the master key to the entire building network. Immediate action is required to change all related locks or passwords.
Developing Emergency Access Control Procedures
Simply having the tool is not enough. Organizations must have strict emergency access control procedures in place. These procedures dictate who can use the tool, under what conditions, and what must happen immediately afterward.
A standard procedure might look like this:
- Trigger Event: System failure X or Safety Alarm Y is activated.
- Authorization Chain: Person A calls Supervisor B. Supervisor B verifies the situation via phone/radio.
- Execution: Supervisor B authorizes Person C (who holds the tool) to proceed.
- Documentation: Person C must document the exact time, action taken, and duration of the bypass.
These procedures ensure that access is never taken lightly, even when speed is necessary. They move the decision-making from one person to a small, accountable team.
When to Use Emergency Access Tools
Knowing when to use emergency access tools separates good security practice from recklessness. These tools are reserved only for genuine emergencies.
| Appropriate Use Case | Inappropriate Use Case (Misuse) |
|---|---|
| Power outage disables electronic door access. | Using the key because you forgot your ID badge. |
| A critical server locks up and fails all logins. | Attempting to bypass maintenance lockout to finish work early. |
| A medical emergency requires immediate entry to a restricted area. | Testing the emergency key to see if it still works. |
| A fire alarm seals all exits, trapping staff inside. | Using override to gain access to a competitor’s documents. |
If an issue can be fixed using standard troubleshooting steps, those steps must be followed first. The emergency tool is the absolute final option before catastrophic failure or prolonged downtime.
Auditing Emergency Access Logs Rigorously
If the tool is used, the record must be impeccable. Auditing emergency access logs is mandatory for compliance and security. This audit checks two things:
- Legitimacy: Was the access used for the stated emergency reason?
- Proper Procedure: Did the user follow all documented steps before and after using the tool?
Audits should happen frequently, not just once a year. They must involve security personnel, system owners, and sometimes internal legal teams. Any deviation from the procedure requires immediate investigation and corrective action.
Security Risks of Master Keys and Centralized Access
Master keys, whether physical or digital, carry significant security risks of master keys. They are single points of failure. If compromised, the damage is widespread.
A single physical master key for an entire office building compromises every lock it opens. A single administrative recovery password for a cloud network compromises every service linked to that account.
To mitigate this risk, modern systems try to limit the scope of any single access credential. Instead of one “master key,” there might be five highly specific “area access keys.” This limits the blast radius if one key is stolen. Organizations must constantly weigh the convenience of centralization against the danger of widespread compromise.
Implementation Best Practices for Emergency Access
Implementing a robust emergency access system requires careful planning far beyond just buying a special key.
H5: Physical Key Management Checklist
- Are keys serialized and tracked in an inventory system?
- Is the lock mechanism regularly tested to ensure the key works under stress?
- Is there a defined process for key decommissioning when a staff member leaves?
H5: Digital Credential Best Practices
- Are emergency digital credentials stored in a dedicated Hardware Security Module (HSM) or secure vault?
- Are these credentials never used for day-to-day operations? (Separation of duties principle).
- Does the system generate an immediate, high-priority alert upon activation of the digital bypass?
Proper implementation ensures that the tool serves its protective function without becoming a threat itself.
Training and Drills: Making Access Second Nature
A key element often overlooked is training. Personnel must practice using the emergency access tools. A drill where a technician attempts to use an override key on a simulated failed lock helps everyone perform better when real pressure hits.
Training should cover:
- The exact location of the tool.
- The correct authorization sequence.
- Post-use reporting requirements.
If staff are unfamiliar with the process, panic during a real crisis will lead to mistakes, potentially making the situation worse. Drills normalize the emergency response.
Legal and Compliance Requirements
Many industries face strict rules regarding access control. Healthcare (HIPAA), finance (SOX), and critical infrastructure have specific rules about how access must be maintained and logged. Failing to follow emergency access control procedures can lead to massive fines. Auditors check these logs regularly to ensure compliance. If the logs show unauthorized access or missing audit trails for emergency uses, the organization fails the compliance check.
Frequently Asked Questions (FAQ)
Q1: How often should emergency access tools be audited?
Emergency access tools and their corresponding logs should be audited frequently, ideally monthly for digital credentials and quarterly for physical keys, or immediately following any reported system failure that required their use.
Q2: Can an emergency key be used for routine maintenance?
No. Emergency keys or override codes should strictly not be used for routine maintenance or convenience. They are for unforeseen critical failures only. Routine access must use standard methods.
Q3: What happens if an emergency key is lost?
If an emergency key or critical digital credential is lost, the entire system protected by that key must be considered compromised. All related locks or digital access points should be immediately changed or rekeyed, and the loss must be reported to senior management and security teams right away.
Q4: Are digital emergency bypasses safer than physical keys?
Digital bypasses can offer better logging and remote revocation capabilities, making them potentially safer overall. However, a poorly secured digital credential poses a huge security risks of master keys because it can be copied or transmitted instantly across networks, unlike a physical item. Safety depends entirely on implementation strength.
Q5: What is the difference between an emergency override and a maintenance mode?
Maintenance mode is a scheduled state where systems temporarily lower their security posture for planned work, usually requiring standard maintenance credentials. Emergency access is unscheduled, immediate access required due to system failure or external critical event, often bypassing maintenance protocols entirely.
